Practical Homomorphic Encryption: Computing on Encrypted Data in 2026

Homomorphic encryption lets you compute on data without decrypting it. Once a theoretical curiosity, it's now fast enough for real applications in healthcare, finance, and privacy-preserving ML.
The Promise of Computing on Secrets
Imagine sending encrypted medical records to a cloud server, having the server run a diagnostic ML model on the encrypted data, and receiving encrypted results — all without the server ever seeing a single plaintext record. The server computes the correct answer without learning anything about the input.
This is homomorphic encryption (HE), and in 2026, it's no longer a theoretical exercise. Performance improvements of 10,000x over the past decade, combined with hardware acceleration and better libraries, have made practical applications viable.
How It Works
Standard encryption is like putting data in a locked box. To compute on the data, you must unlock the box, perform the computation, and re-lock it. The data is exposed during computation.
Homomorphic encryption is like putting data in a locked box with built-in robotic arms. You can manipulate the data through the arms without ever opening the box. The result is still inside the locked box — only the key holder can read it.
Mathematically, an encryption scheme E is homomorphic if:
- Addition: E(a) + E(b) = E(a + b)
- Multiplication: E(a) × E(b) = E(a × b)
Since any computation can be expressed as a combination of additions and multiplications, a scheme that supports both operations can compute any function on encrypted data. This is called Fully Homomorphic Encryption (FHE).
The Three Flavors
Partially Homomorphic (PHE)
Supports either addition or multiplication, but not both. RSA is partially homomorphic for multiplication. Paillier encryption is partially homomorphic for addition. These have been practical for decades but limited in scope.
Somewhat Homomorphic (SHE)
Supports both operations but only for a limited number of operations before noise accumulates and decryption fails. Useful for specific bounded computations like simple statistics.
Fully Homomorphic (FHE)
Supports unlimited operations through a technique called bootstrapping — periodically refreshing the ciphertext to reduce accumulated noise. This is the general-purpose version, and the one that's become practical.
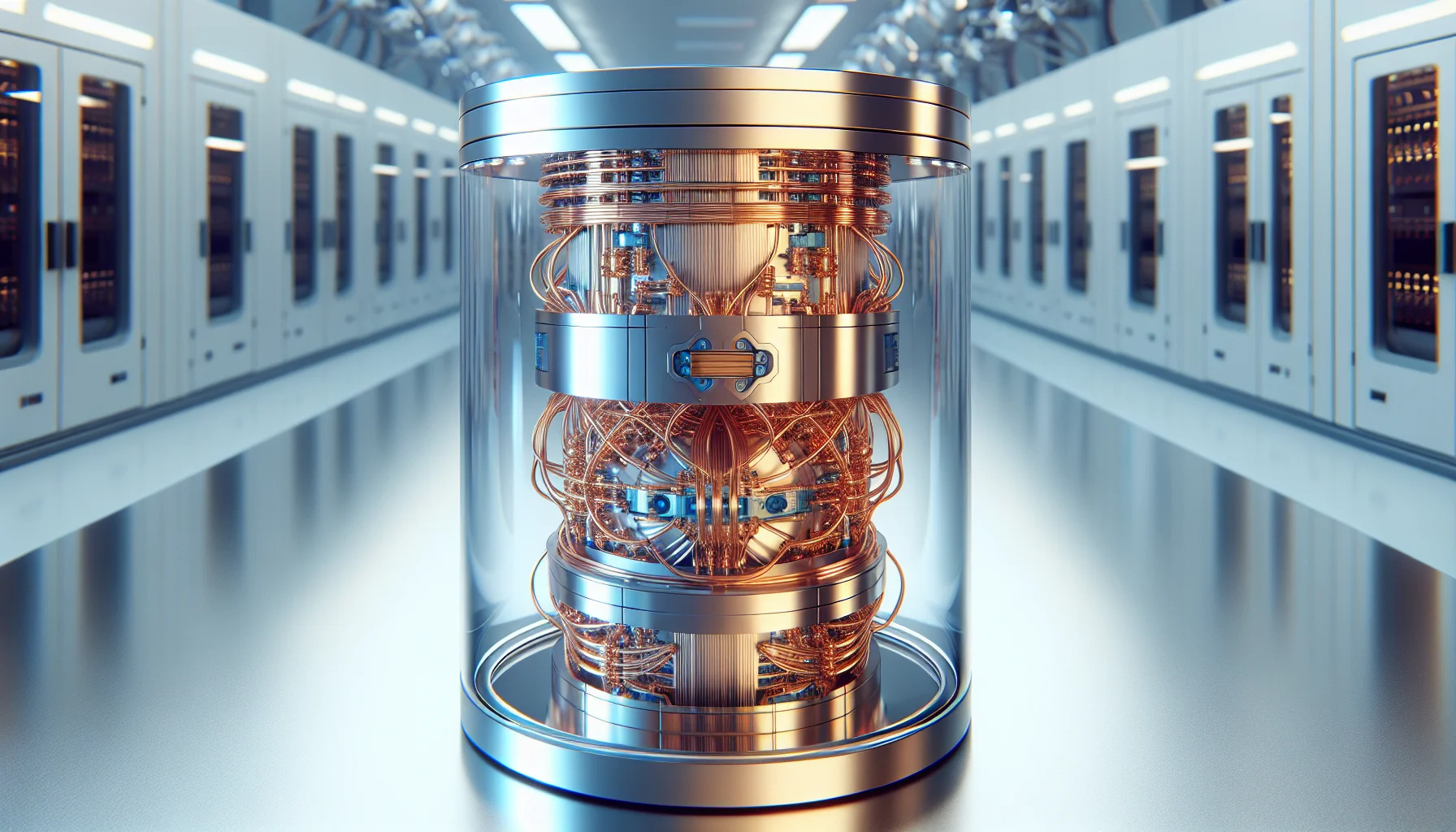
What's Changed: Why FHE Is Practical Now
Craig Gentry's original FHE scheme (2009) was roughly 10 trillion times slower than plaintext computation. That's not a typo. Computing a single bootstrapping operation took 30 minutes.
Today's state of the art:
- CKKS scheme (Cheon-Kim-Kim-Song) enables approximate arithmetic on encrypted real numbers, perfect for ML and statistical workloads
- GPU acceleration speeds up FHE operations by 100-1,000x compared to CPU-only
- FPGA and ASIC development by companies like Zama, Duality, and Intel promises another 10-100x speedup
- Modern FHE libraries (OpenFHE, SEAL, Concrete) reduce the overhead to 1,000-10,000x plaintext speed for many practical workloads
A 10,000x overhead sounds terrible — but for batch processing where privacy is mandatory, it's acceptable. Running a diagnostic model over 10,000 encrypted patient records in 10 minutes instead of 0.06 seconds is a reasonable tradeoff when the alternative is "don't do it at all because of HIPAA."
Real Applications in 2026
Healthcare Analytics
Multiple hospitals can pool encrypted patient data for collaborative research without sharing individual records. A cancer research consortium can train models on encrypted tumor genomics data from 50 hospitals, with no hospital seeing another's patients. This is actively deployed in several European healthcare networks.
Financial Fraud Detection
Banks can collaboratively detect fraud patterns across institutions without sharing customer transaction data. Each bank encrypts its transactions, a central model runs on the encrypted aggregate, and each bank receives encrypted results relevant only to their customers.
Privacy-Preserving Machine Learning
Tools like Zama's Concrete ML allow training and running ML models entirely on encrypted data. The model owner never sees the data, and the data owner never shares plaintext. This enables ML-as-a-service for sensitive domains that were previously impossible.
Getting Started
For developers interested in FHE:
- Start with Concrete by Zama — a Python library that compiles regular Python/NumPy code to FHE circuits. It's the most developer-friendly entry point.
- Microsoft SEAL for lower-level C++ implementations with full control over parameters.
- OpenFHE for research and advanced use cases, supporting all major FHE schemes.
- Understand the noise budget — the key constraint in FHE. Every operation adds noise; when noise exceeds the budget, decryption fails. Designing efficient FHE computations means minimizing the multiplicative depth of your computation.
The Road Ahead
FHE won't replace standard encryption for most use cases — the overhead is still significant. But for the growing class of problems where "we need to compute on data we're not allowed to see," FHE is transitioning from impossible to practical. The gap between theoretical capability and production readiness is closing faster than most people realize.
References & Citations
- Gentry, C. (2009). "A Fully Homomorphic Encryption Scheme." Stanford PhD Thesis.
- Cheon, J.H. et al. (2017). "Homomorphic Encryption for Arithmetic of Approximate Numbers." ASIACRYPT 2017.
- Zama (2025). "Concrete ML: Privacy-Preserving Machine Learning." Technical Documentation.
Related Posts

SITUS Protocol: Sensor-Integrated Trust Using Spatial Entropy — Authentication Bound to Physical Reality
Current authentication proves who you are, but not where you are. SITUS Protocol introduces Environmental Entropy Vectors — a cryptographic primitive that binds every authentication event to the unrepeatable physical context in which it occurs. Credentials become non-relocatable.
Zero-Knowledge Proofs Are Going Mainstream: What Developers Need to Know
ZK proofs used to be academic curiosities. In 2026, they're in production identity systems, blockchain rollups, and privacy-preserving analytics. A practical guide for developers entering the space.
Post-Quantum Cryptography: Migrating Before It's Too Late
NIST has finalized post-quantum standards. The harvest-now-decrypt-later threat is real. Here's a practical migration roadmap for engineering teams that can't afford to wait.